Secure communication and private messaging with End-to-end encryption
Introduction
Secure communication
Secure website browsing is indicated using the HTTPS (Hypertext Transfer Protocol Secure) where data is sent secure via Transport Layer Security protocol (TLS) which provides three key layers of protection
- Encryption - transform the plain text to cipher text (unreadable)
- Integrity - data can not be modified or corrupted without being detected
- Authentication - make sure you communicate with the intended website and not a fake one
To ensure the website you are browsing uses HTTPS and comply with the three key layers of protection, In the browser address bar a lock icon next to the website name should appear.
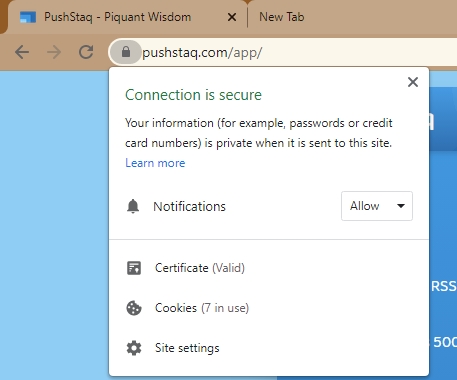
PushStaq as an example for secure connection in the browser address bar
End-to-end encryption
Although secure connection makes sure the connection between user and a server is private and secure, The data between the user and the server is visible to the server.
End-to-end encryption (E2EE) is a system of communication where only the communicating users can read the messages. In principle, it prevents potential eavesdroppers – including telecom providers, Internet providers, and even the provider of the communication service – from being able to access the cryptographic keys needed to decrypt the conversation.[1]
End-to-end encryption is intended to prevent data being read or secretly modified, other than by the true sender and recipient(s). The messages are encrypted by the sender but the third party does not have a means to decrypt them, and stores them encrypted. The recipients retrieve the encrypted data and decrypt it themselves.
quoted from Wikipedia End-to-end encryption
To summarize, When a user send a message it is sent encrypted, When the same user or other user that receives the message from a different device they decrypt the message themselves. All this without the server knowing what is the message content since it is encrypted.
PushStaq Security and End-to-end encryption
By default PushStaq communication is secured with HTTPS at all times.
But what if you wish to have all your messages private and hidden from everyone and make sure that they are not monitored by any 3rd party? even from PushStaq servers.
PushStaq offers End-to-end encryption messaging, To enable this you will need to enter a password in your channel settings.
Entering a channel password creates a special encryption secret key that is saved on user device which is never sent to PushStaq servers.
All channel communication will be now encrypted using the password, this means that your message will be sent encrypted to all of your other devices.
When viewing the channel from your other devices you will need to enter the same password in order to decrypt the message and view it.
PushStaq just forwards your messages and let your devices to handle the encryption and decryption process.
When subscribing to a channel that is encrypted to receive real time push notifications, The push notification message is fully encrypted with the channel password as well (additional encryption that is on top of the existing Push notification Message Encryption for Web Push standard security).
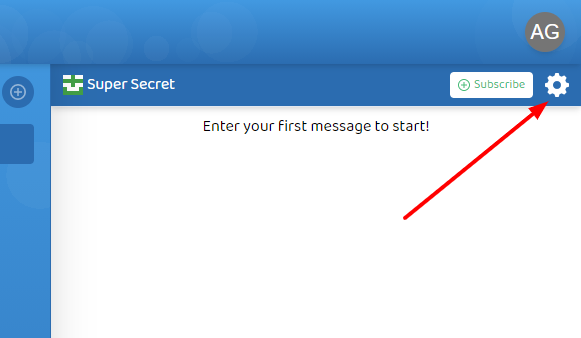
Setup
-
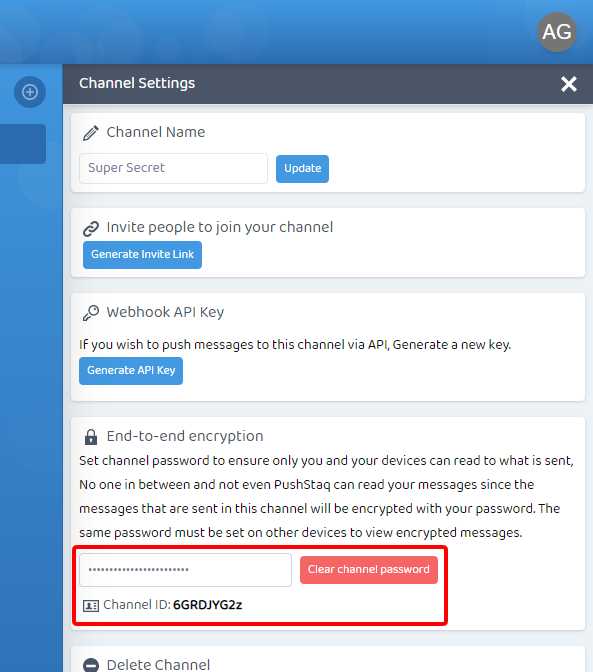
Create a channel or select existing one you would like to enable End-to-end encryption. In the selected channel, click the top right settings icon to open the settings pane.
-
In the Settings pane section
End-to-end encryptionSet a new channel password (write it down in somewhere safe) and clickSet channel password. From now on the channel communication will be fully encrypted. In order to view encrypted messages on other devices you will need to enter the same password in your other devices as well.
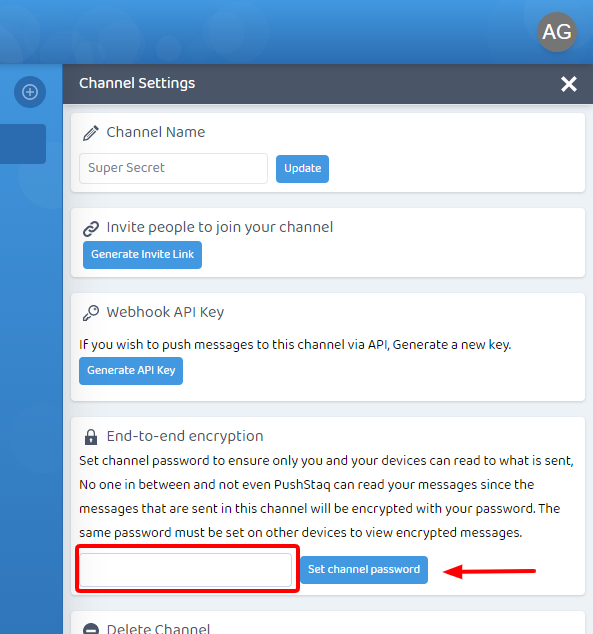
After your password is set, If you wish to change or clear channel password click
Clear channel password.
-
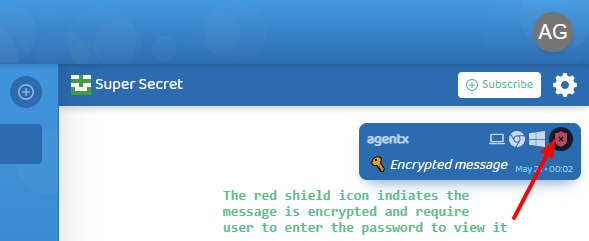
To verify that messages sent are encrypted, on every message an encryption status icon is attached.
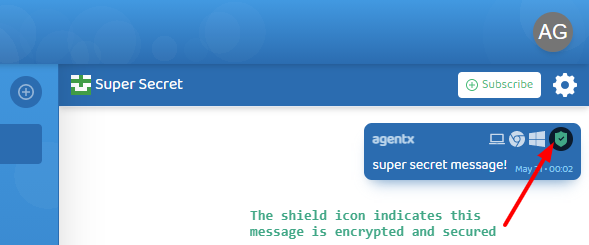
On other devices (or users who share the same channel), if you don't set the password, the message will indicate it is encrypted and a password is required to view the message content.
-
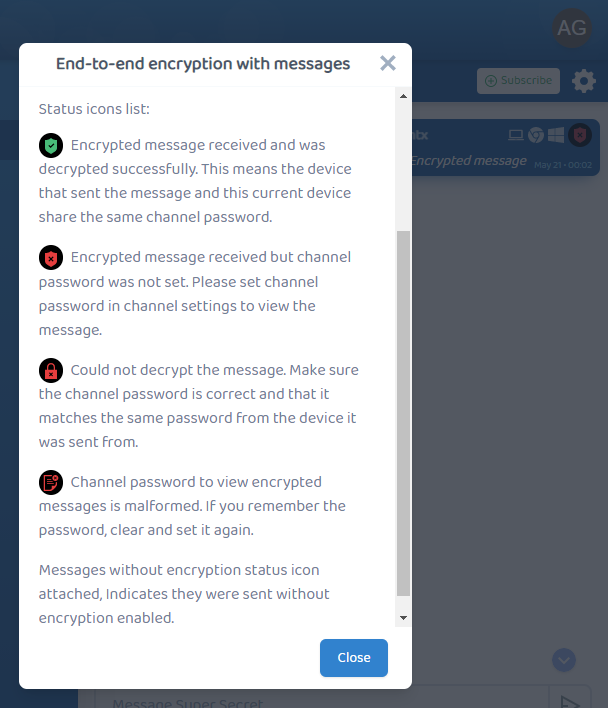
To learn more about the encryption status of messages, click on the encryption status icon. this will open a popup modal with a more detailed info on each status.
✨ Thats its! ✨
Encryption methods used
** Warning **, Nerdy content 🤓
When entering a channel password, PushStaq client (Browser webcrypto API) make use of PBKDF2 (A key derivation function) to generate a special key called the derived key (which is hard to guess) to be used as a cryptographic key for AES-256 (Advanced Encryption Standard) encryption algorithm with 256 bits key length (largest bit size which is hard to break using brute force).
As well Applied GCM Mode (Galois/Counter Mode) for authenticated mode, This means that it includes checks that the encrypted message has not been altered by any other entity.
Conclusion
In this guide we learned about secure communication and End-to-end encryption and how to use it with PushStaq.
Related posts
Discuss this post on Reddit
Feedback
If you have any feedback, Suggestions or any other questions feel free to Discuss on PushStaq official subreddit
or contact us at hello[at]pushstaq.com